Security
We provide services compliant with strict technical, structural, and security standards
Monitoring privileged users
When ensuring an appropriate operation of key systems of an organisation, privileged users are indispensable. However, their access privileges pose a significant security risk as due to these privileges they may cause both intentional and unintentional damage.
It is very complicated to solve this problem since:
- limiting the access of the privileged users would require extensive and costly changes within already existing systems,
- withdrawal of the authorisation would decrease their ability to respond to states of emergency,
- auditing of the systems is mostly not sufficient to determine what has actually happened within the system; its extension poses essential operation problems and requires substantial investments.
The system provided by our company, aimed at monitoring of the privileged users, assists in reducing potential risks and privileges abuse occurrence, while being more of a detterence factor than an actual interference in the operation as such. It enables tracking the users within the production systems, while offering an option of retrospective proof.
Basic characteristic
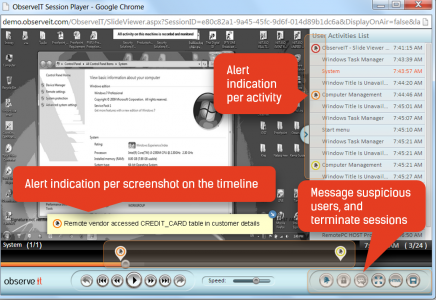
- real-time visual record of activities kept outside of the monitored system
- it does not influence the operation
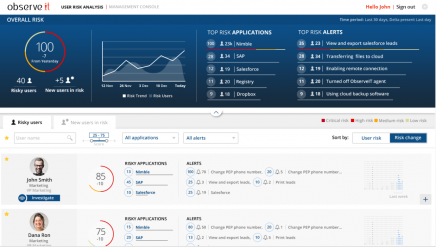
- risk profile evaluation on the basis of user´s activities
- automatically generated notifications in case of unusual or risky activities
- it functions as a so-called detterence factor
Needs analysis and a proposal of the solution
Implementation of the privileged users monitoring system
Consulting provided with analysing of security incidents that involve abuse of the privileged access
It creates real-time visual record of activities kept outside of the monitored system
It evaluates the risk profile on the basis of user´s activities
It automatically generates notifications in case of unusual or risky activities
Visual documenting of performed changes – thus it is easier to reproduce the changes
Searching in activities records